IT Infrastructure Security

✔️ Windows
✔️ Linux
✔️ Secure virtualization

✔️ Encryption
✔️ RAID
✔️ Permissions
✔️ Server room
✔️ Badges
✔️ Access rights

✔️ Monitoring
✔️ Window
✔️ Supervision
Advanced features configured
Server firewall
Configure advanced filtering rules to protect your servers from unauthorized access.
Blocking sensitive ports
Close unused ports and restrict access to critical services (RDP, SSH, SQL).
Strict permissions
Fine-grained management of access rights based on the principle of least privilege.
Antivirus server
Real-time protection against malware, ransomware, and advanced threats.
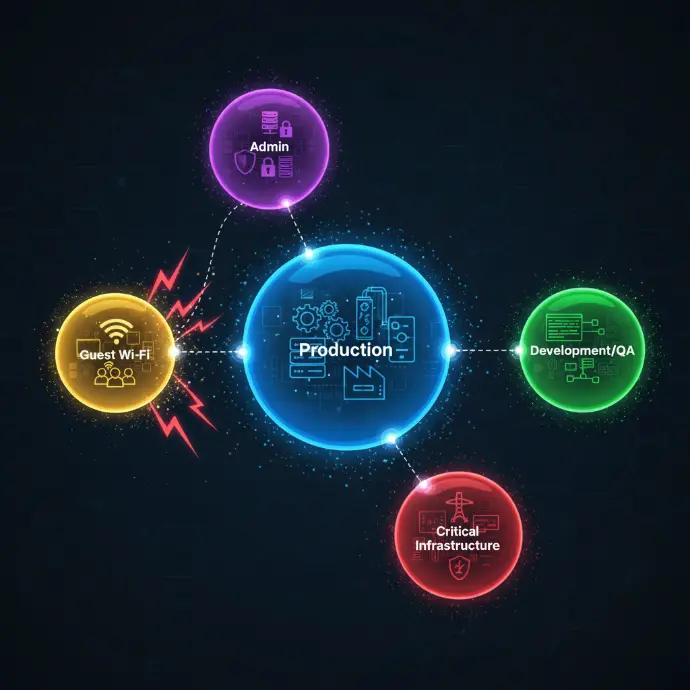
Isolation VLAN
Network segmentation to isolate critical servers and limit the spread of threats.
Isolated backups
Offline or air-gapped backups for ransomware protection.
Vulnerability scans
Regular analyses to detect security vulnerabilities and proactively correct them.
Security process
Complete infrastructure audit
In-depth analysis of your infrastructure: servers, network, storage, access, and configurations.
Identification of vulnerabilities and risks
Detection of vulnerabilities, misconfigurations, and potential entry points for attackers.
Implementation of a security plan
Definition of a prioritized action plan with security measures to be implemented.
Installation of protective devices
Deployment of security solutions: firewalls, antivirus software, EDR, network segmentation.
Internal penetration testing
Simulation of attacks to validate the effectiveness of the protections put in place.
Documentation & Network Diagram
Creation of technical documentation and secure architecture diagrams.
Maintenance & continuous monitoring
24/7 monitoring, security updates, and incident response.

Hardening of servers and critical environments
We apply strict standards to secure your environments:
hardening Windows Server & Linux
limited administrator access permissions
system monitoring
RDP/SSH restriction
antivirus/EDR server
centralized logs and journals
Equipment & technologies we use











Most companies are vulnerable without knowing it
90%
Attacks target poorly configured infrastructure.
Protect your infrastructure from threats and ensure business continuity.


Securing your company's network
We audit, configure, and strengthen your internal network:
business firewall
segmentation (VLAN)
flow filtering
intrusion protection
secure VPN access
isolation of sensitive servers
FAQ – Infrastructure Security
Protect your IT infrastructure from cyber threats with our advanced security solutions.
Infrastructure security consists of protect your servers, networks, equipment, and data against cyberattacks, outages, and unauthorized access. This is the base of your IT security, without which your entire business is vulnerable.
We protect against numerous threats : cyberattacks (ransomware, malware), intrusions, denial of service (DDoS), data theft, hardware failures, human error. An approach multilayer for complete protection.
We deploy several tools : next-generation firewalls, intrusion detection systems (IDS/IPS), server antivirus software, encryption, access management, 24-hour monitoring, automatic backups, and continuity plans.
We are implementing continuity plans (BCP/DRP) : regular backups, data replication, backup servers, tested recovery procedures. In the event of an incident, your business will be up and running again quickly.
Yes, we do comprehensive security audits : analysis of your infrastructure, identification of vulnerabilities, penetration testing, prioritized recommendations. Auditing is the first step toward secure your IT effectively.
Develop the skills of your teams
Cybersecurity & User Best Practices
Collaborative tools & digital organization
ERP, CRM, DMS & automation
Cloud, infrastructure & telephony
GDPR Compliance & Data Security
🎓 Discover our Training Courses →
Train your teams on essential IT challenges.
Our latest content
Discover what's new in our company!
Port & Vulnerability Scanner
Discover the open ports and vulnerabilities exposed on an IP address. Instantly check whether your infrastructure is visible from the Internet using the database. Shodan.
🔍 Data provided by Shodan InternetDB — Global Internet scan database.
 Free IT audits · Certified cybersecurity · Secure cloud
Free IT audits · Certified cybersecurity · Secure cloud



