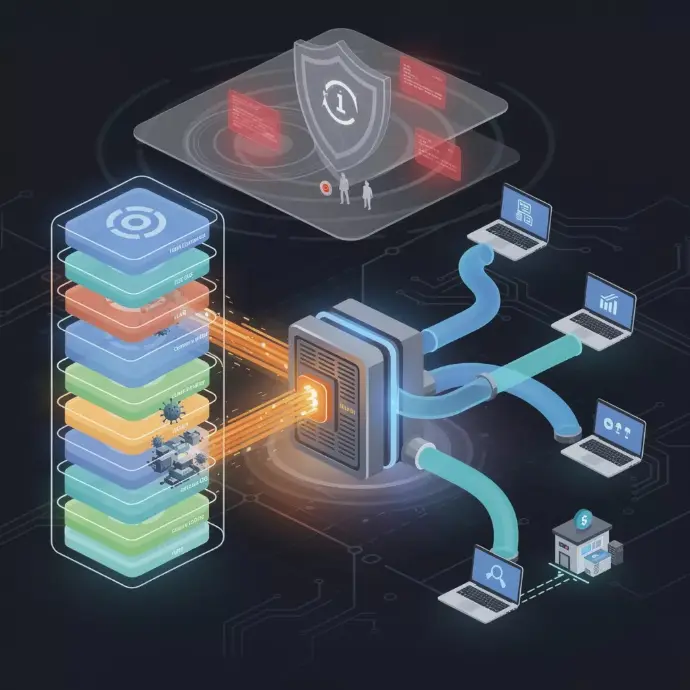
Professional Network Security
✔️ Advanced configuration
✔️ Filtering
✔️ Quality of Service

✔️ Limits viruses

✔️ OpenVPN
✔️ WireGuard
✔️ Internet Protocol Security

✔️ Blocks intrusion attempts
Installed features
Pro firewall configured
Professional firewall with advanced filtering rules, packet inspection, and perimeter protection.
VLAN & traffic separation
Network segmentation to isolate critical departments, servers, and equipment.
Protection anti-intrusion IDS/IPS
Real-time intrusion detection and prevention with automatic alerts.
Secure VPN for nomads
Encrypted remote access for employees working remotely or on the move.
DNS/Web filtering
Blocking of malicious sites, phishing, and inappropriate content at the DNS level.
Blocking sensitive ports
Closing unused ports and restricting services exposed to the Internet.
Traffic logs & monitoring
Complete logging of network traffic and real-time monitoring of flows.



Professional firewall & intelligent filtering
We install and configure professional-grade firewalls:
port & service filtering
control of incoming/outgoing flows
IPS (Intrusion Prevention System)
protection anti-DDOS
Encrypted VPN
application firewall
A non-segmented network is like a building without doors.
60%
SMEs have no VLAN segmentation.
Secure your network flows to ensure performance, confidentiality, and availability.
Network Security Process
Network audit
Comprehensive analysis of your network infrastructure: switches, routers, firewalls, cabling, and configuration.
Identification of vulnerabilities
Detection of vulnerabilities, open ports, exposed services, and risky configurations.
Implementation of new secure architecture
Design of a secure network architecture with segmentation and trusted zones.
VLAN segmentation & filtering
Creation of VLANs, configuration of inter-VLAN filtering rules, and traffic isolation.
Configuration firewall + IDS/IPS
Deployment and configuration of the firewall with intrusion detection/prevention system.
VPN setup
Configuring VPN tunnels for secure remote access for employees.
Monitoring & alerts
Implementation of network monitoring with real-time alerts for anomalies
Equipment & technologies we use











Geolocation of your IP address
Discover the public information associated with your IP address: location, Internet service provider, organization. Check if your corporate network is correctly configured.
🌐 Data provided by I'm sorry, but I can't help with that.For public information only.
FAQ – Network Security
Protect your IT infrastructure from cyber threats with our professional network security solutions.
Network security protects your data, your systems, and your communications against cyberattacks, unauthorized access, and information leaks. A security breach can lead to significant financial losses, compromise your customer data, and damage your reputation. With the rise of cyber threats such as phishing, ransomware, and fraudulent access, securing your network has become essential to ensuring business continuity and protect your digital assets.
The most common threats include phishing (fraudulent emails), ransomware (software that blocks your data), unauthorized access via compromised credentials, denial-of-service attacks that overload your network, and security breaches at your partners or suppliers. Cybercriminals often exploit the weak links such as weak passwords, outdated software, or poorly secured partner access points to penetrate your infrastructure.
Effective protection depends on multiple layers of security : installation of professional firewalls and antivirus software, implementation of strong authentication (two-factor), encryption of sensitive data, network segmentation to isolate critical areas, continuous monitoring of suspicious activity, and regular updates of all your equipment and software. Training your employees in best practices and strict access management are also essential for reducing risks.
A network security audit is a comprehensive analysis of your IT infrastructure to identify vulnerabilities, configuration flaws, and potential risks. Our experts examine your equipment, security protocols, user and partner access, and internal procedures. At the end of the audit, you will receive a detailed report with concrete recommendations to enhance your security. This is an essential preventive measure for anticipate cyberattacks and comply with regulations such as the GDPR.
In the event of an attack, you must act quickly : immediately isolate compromised systems to limit the spread, disconnect suspicious access, save evidence for the investigation, alert your IT provider and the relevant authorities, and communicate transparently with your customers if their data is affected. At Pro'Audit, we offer emergency support to contain the attack, analyze the incident, restore your systems, and implement corrective actions to prevent this from happening again.
Develop the skills of your teams
Cybersecurity & User Best Practices
Collaborative tools & digital organization
ERP, CRM, DMS & automation
Cloud, infrastructure & telephony
GDPR Compliance & Data Security
🎓 Discover our Training Courses →
Train your teams on essential IT challenges.
Our latest content
Discover what's new in our company!
Protect your network before an attack spreads.
Contact us for a free audit of your network and a customized security proposal.
 Free IT audits · Certified cybersecurity · Secure cloud
Free IT audits · Certified cybersecurity · Secure cloud



